
hack
BT Home Hub Hacking (old)
January 1, 2012
Please respect the license under which this work is made available. (See terms and conditions at the end of the page)
First a disclaimer: You must fully understand the risks involved in carrying out procedures on this page. I am not responsible for anything that may happen to anyone or any property as a result of following instructions on this page. If you’re not comfortable with this then don’t read any more.
Random information about BT home hub. Version of the hub abused here is 1.5.
Random information about the BT Hub Phone can be found on this page
How to disassemble
To complete this procedure you’ll need a Philips screwdriver, a flat screwdriver and a scalpel. (You can skip the scalpel if you don’t care about the label on the back - just rip it off!)
Carefully remove label on the back covering the screw using a scalpel or something similar. (See this picture)
Undo the screw.
Carefully remove the rubber feet. You can use a flat screwdriver to help lift them away. (See this picture)
Remove the two screws and pull the case apart.
To remove the PCB, lift at the end where the sockets are. It might help to disconnect P8 and P14 antenna connectors.
What’s inside?
Inside the hub theres a well populated PCB, a couple of additional antennas and connection to the hub phone front socket. The picture to the right shows one side of the PCB. The IC’s are listed below.
PCB Side A
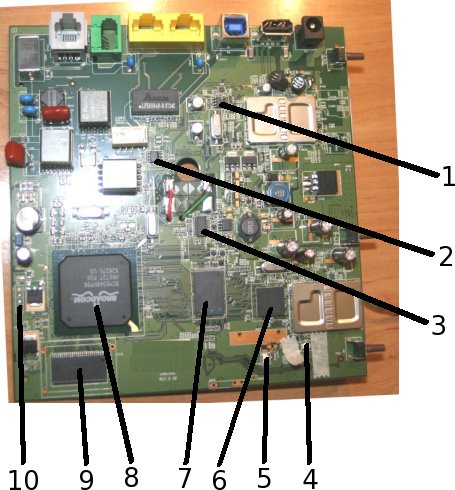
- IC4 = ST 24C64WP - 64kbit (8kbyte) serial EEPROM. This may contain the code for the ARM processor on the other side of the board
- IC24 = ST E9726 (Not sure what that is)
- IC21 = Appears to be a i6420 PWM controller perhaps used as part of the power supply for the microcontrollers
- P8 = Internal antenna connection.
- P14 = External antenna connection.
- IC27 = Broadcom BCM4318EKFBG WiFi transciever
- IC9 = S29GC064A 64-Mbit (8Mbyte) flash memory
- Main CPU = Broadcom BCM6348KPBG
- IC16 = Qimonda HY8395C256160FE-7 - 256-Mbit (32Mbyte) DRAM
- P2 = 3.3V TTL Serial port.
(Note voltage - never connect directly to a PC serial port!)<ul><li>Pin 1 = GROUND / 0V</li> <li>Pin 2 = RXD (Input)</li> <li>Pin 3 = TXD (Output)</li> <li>Pin 4 = Vcc (3.3V)</li> <li>Baud Rate: 115200bps</li> <li>Other: 8N1 (8-bit, No Parity, 1 stop bit)</li> </ul> </li>
PCB Side B
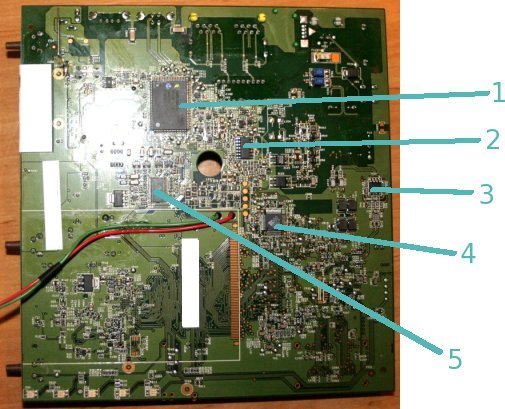
- IC2 = NXP PCD80705 ARM7 Microcontroller
- IC26 = HCT4066 Quad switch
- IC14 = Broadcom 6301KSG ADSL2+ Line driver
- IC8 = ALTIMA AC101LKQTG Ethernet transciever
- IC1 = Si3230-FT - I think this is a SLIC for the analog phone port
- P3 = Possible JTAG port (see below)
Firmware bootup (bootlog)
This boot log was taken from the serial port on P2.
Bootup keypresses: Sending Ctrl+C during this sequence seems to kill the init routine dead resulting in the main application starting early. Sending it just after the nmon kernel module has loaded results in the application starting with the comment “[ERROR]: An illegal build is trying to run!” (What’s illegal about that?!) Sending Ctrl+Q when bootup has completed turns on lots of application level debugging information. I can’t login at the console with the latest firmware.
JTAG
On the reverse of the board, there is a small 8-pin connector footprint sited directly under the CPU. Googling about indicates this may be a JTAG port (2=TDI=TP33, 3=TDO=TP32, 5=TMS=TP34, 6=TCK=TP35) but I have not tried this yet
- it’s next! It was indicated that reading the firmware can be accomplished with a strangely named utility and a simple parallel port cable. See here
Recovery Mode
Holding down the Wireless Assoc button during poweron for about 5 seconds puts the device into firmware recovery mode. The device will attempt to acquire from a BOOTP/DHCP server, an IP address, TFTP filename and TFTP server. If it gets all these things it will download the file and use it. Giving it the .BLI file from BT’s recovery zip file results in a firmware upgrade. (Status information is outputted to the console during the upgrade process.)
Recovery File (.BLI) File Format
I’m not yet sure of the format of this file. Feeding the device with a couple of “random” experimental files indicate:
The BLI part at the beginning of the file indicates the file type to the bootloader - providing a file that doesn’t begin with BLI (such as a Linux kernel… we should be so lucky eh?!) results in the download being aborted.
The file appears to have some header information after the initial BLI part. Making a random mod to this header resulted in errors about a “Seal…” sigh is it encrypted or is this just a checksum.
Modifying a byte somewhere in the middle of the file results in the whole file being downloaded but it still won’t flash.