
review
OATH OTP Token Review and Library
January 1, 2012
I have always considered plain passwords to be extremely insecure as they are vulnerable to key loggers, shoulder surfing and other techniques which instantly render them useless.
A simple defence is to make sure you only use a password once. Using a OTP token is one way to achieve this.
This page presents an OATH OTP library and test program for Python.
Hardware testing
I have tested this library against hardware tokens (C100 OTP and C200 OTP from Feitian)
Importance of keeping the key secret
The security provided by OATH OTP tokens rests on the secrecy of the seed/key.
For event based tokens such as the C100, knowledge of the key by an attacker is not in itself useful without knowledge of the internal counter value (i.e. how many times the button has been pressed.) However this information can be obtained quickly - you need just one or two passwords from the device to be able to work out the internal counter value.
For time based tokens such as the C200, knowledge of the key enables an attacker to immediately clone the token.
Both these attacks can be demonstrated using the program below.
Security limitations of C100, C200 and others
The tokens I purchased have had their keys set at the factory. The tokens are then delivered with this key information sent on printed paper.
For reasons stated above, this key is critical security information and it should be known only by the token and the authentication server. In this case however, the key is known and stored by at least two external parties; the factory and the vendor.
There is no way for the end user to change this key.
Makers of these tokens should provide a way to set the key. Or, preferably for the device to be able to internally generate and show a new key on demand. Internal generation is preferred because it prevents someone from making a cloned token but at the same time gives them the security of a key not known externally.
I am told by the vendor that such tokens do not yet exist.
A peek inside a C100 token
Curiosity got the better of me.
The specification for these devices describes the casing as “tamper evident.” I had no trouble dismantling the token in a non tamper-evident manour with nothing more than a screwdriver.
The PCB has the battery soldered on board with a globbed CPU and the display soldered on the reverse. The 3x3 pads on the right line up with a hole in the back of the casing (normally covered up by a plastic cover.) This must be where it is programmed. (Looking closely shows indent marks on the pads.) Obviously, one has to wonder if it is possible to read the seed back out of this port. There is another port on the display side.

I deliberately reset the device by momentarily shorting the battery. After a second of displaying all 8’s, the display shows as below :
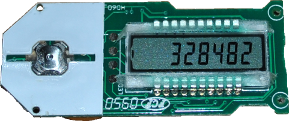
This appears to show the seed has been deleted as pressing the button reads “Err 1.” The only pads I can identify on the 3x3 are GND, VBAT, RESET(possibly), nBUTTON and an unknown output. One isn’t connected and 3 others may be inputs. The output goes high during reset. Any clues how to re-initialise the token are welcome!
Python OATH OTP Library and Test Program
To understand how these devices work, I wrote a quick library and test program based on the applicable standards. You can import this library into your own programmes or simply run it to access the interactive test program.
Example output from test program:
